About Okta
Okta is a cloud identity and access-management platform that lets organisations securely manage users, groups and application access. Connecting Okta to Serval enables zero-touch provisioning, access reviews and incident-response workflows directly from chat.
What the Okta integration enables
| Capability | Description |
|---|
| Access Management | Create, update, and manage users and groups |
| Automation workflows | Streamline identity lifecycle management, provision users to applications via groups, and more |
Installation Methods
There are two ways to connect Okta to Serval:
- Okta Integration Network (Recommended) - Install directly from the Okta app catalog for a streamlined setup experience
- Custom App Integration - Manually create an API Services app for more granular control over permissions
Option 1: Okta Integration Network (Recommended)
The fastest way to connect Okta to Serval is through the Okta Integration Network (OIN) app catalog.
1. Install Serval from the Okta App Catalog
- Log into your company’s Okta admin console
- Navigate to Applications > Applications
- Click Browse App Catalog
- Search for “Serval” and select it (or go directly to the Serval integration page)
- Click Add Integration
2. Authorize the Integration
- On the authorization page, review the requested API scopes
- Click Install and Authorize
- Okta will generate a Client ID and Client Secret for your organization
- Important: Copy the Client Secret immediately - it will only be shown once
3. Complete Serval Configuration
- In Serval, navigate to Applications and click Connect New +
- Find the Okta integration and click Connect
- Enter the following details:
- API Domain: Your Okta domain (e.g.,
mycompany.okta.com). Do not include -admin if you’re copying from the admin console URL.
- Client ID: The Client ID provided when you authorized the integration
- Client Secret: The Client Secret provided when you authorized the integration
- Scopes: Enter the following comma-separated scopes:
okta.apps.read, okta.apps.manage, okta.users.read, okta.users.manage, okta.groups.read, okta.groups.manage, okta.logs.read
Your Okta integration is complete. Confirm the integration is configured correctly by running the health checks in the API Integration tab.
Option 2: Custom App Integration
Use this method if you need more granular control over permissions, want to create custom roles, or if the OIN app is not available in your region.
1. Create App Integration
- Log into your company’s Okta admin console
- Navigate to Applications > Applications
- Select
Create App Integration
- Title the app “Serval” (this can be any value, but make sure to give it a title that helps you remember that this application is for integration with the Serval platform.
- Hit Save & Finish creating the app integration.
- Next, you will need to grant this app integration an admin role. Navigate to Admin roles and hit Edit Assignments.
-
You must now assign roles to the application. Here is an article which explains the difference between roles and scopes. You can select one of the following options:
- Grant Serval the
Super Administrator role. This will allow Serval to access all resources in your account, but only using the API scopes you configured previously.
- Assign another set of predefined roles. We recommend “Group Administrator”, “Organization Administrator” and “Application Administrator” at a minimum. Here is an article which outlines the different permissions which can be accessed with these roles.
- Create a custom role. This option can be used if you want to configure fine grained permissions for Serval. Again, API scopes also govern which actions Serval can take in your Okta account.
-
Optionally, you can create a new role.
- If you’ve chosen to create a new role, grant it the permissions you want Serval to be able to perform.
- Now you will need to assign a resource set to this role. Add an assignment, select the ones you like, and hit Save Changes
- If you don’t already have an applicable resource set, you can create a resource set for this admin role to have control over. Navigate to Security → Administrators and then select the resources tab. Select Create a new resource set. Select the resources you want Serval to be able to manage and hit Create.
3. Complete app integration configuration
- In general settings, uncheck the box requiring DPoP and hit Save. We do not currently provide PoP.
- Next, configure the client credentials. We use the private key/public key method for added security. Make sure your configuration looks like this:
- Next, select
Add Key and then generate one. Copy the JSON **data to your clipboard and select Done.
- Note: Just because a key was generated does not mean it was saved, the key does not save until you select Done. Please verify that a key was actually created & saved.
4. Complete Serval Configuration
- In Serval, navigate to
Applications and click Connect New +. Find the Okta integration and press Connect.
- Copy the JSON from the last step into the
Client Secret section.
- Your Instance ID should be the domain of your okta instance, so if your okta is found at
https://mycompany.okta.com/, your instance ID would be mycompany.okta.com . If you are in the admin console, do not include the -admin in this (i.e. mycompany-admin.okta.com)
- Your Client ID can be found at the top of the app integration page:
- Enter scopes. The scopes you enter should be a comma separated list of what you granted the application previously in Okta. See Default API Scopes for the recommended scopes to include.
- Click
Submit
- You should now be able to build or install workflows which leverage Okta APIs, e.g. you could build a workflow for creating a new Okta group or a new user.
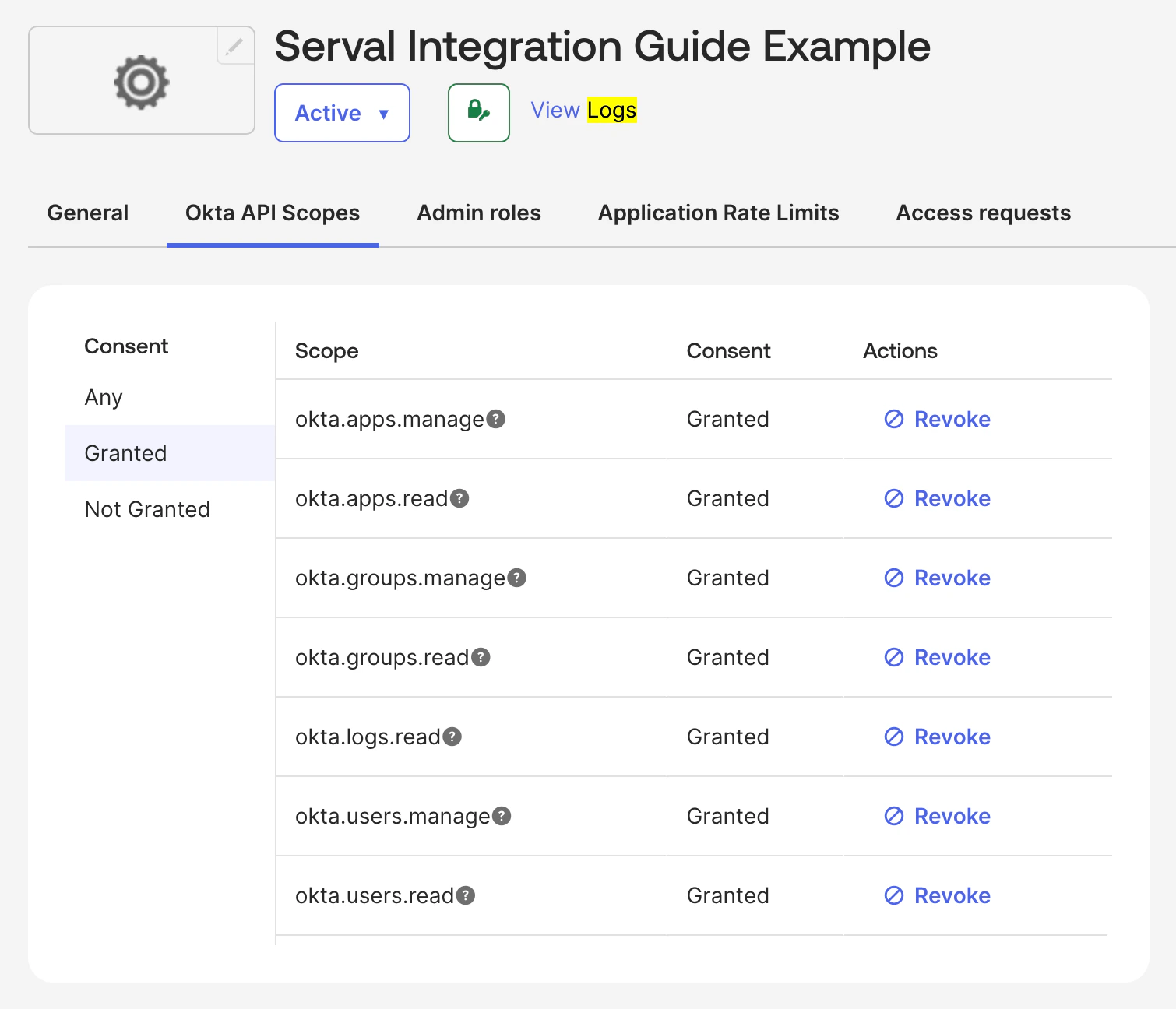
Default API Scopes
The Serval OIN integration requests the following OAuth 2.0 scopes by default. You can copy the scopes below for use in the Serval configuration:
okta.apps.read, okta.apps.manage, okta.users.read, okta.users.manage, okta.groups.read, okta.groups.manage, okta.logs.read
| Scope | Description |
|---|
okta.apps.read | Read access to applications in your Okta organization |
okta.apps.manage | Create, update, and delete applications |
okta.users.read | Read access to user profiles and attributes |
okta.users.manage | Create, update, and delete users |
okta.groups.read | Read access to groups and group membership |
okta.groups.manage | Create, update, and delete groups and manage membership |
okta.logs.read | Read access to system logs for auditing and monitoring |
Support
If you need assistance with the Serval Okta integration, please contact us at support@serval.com..png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=c215292d189f3f60551931be48f2701f)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=9da992dea695c6ce18ec4ff914529e12)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=4e5e7378231f8a91c9b321196970700f)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=957182eac19bededbcb808713c4967d3)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=565f65fe25c185267e5024d7f538bff1)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=0950c4865c27b26471d389a1af48c843)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=73a5e74d1572094dc2003a1f5bf9c5b7)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=4d9c609c5d710f041b7cc03cebf0314c)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=3fcc5ad8eb2931c59f41136927e4b41e)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=e0266439cb4ce79e3392e53eb1d84b7b)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=85e9497466154b02832d918c5a18dfa8)
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=da9e5fb0d93d10f24c3d7d9ab24e0443)