About AWS
Amazon Web Services (AWS) is a public-cloud platform, offering on-demand compute, storage, database, and networking services. Connecting AWS to Serval lets you automate everyday cloud-ops and security workflows—from listing IAM roles to spinning down unused EC2 instances—directly from chat.What the AWS integration enables
| Capability | Description |
|---|---|
| Access Management | Create, update, and manage users and their permissions |
| Automation workflows | Manage resources, create roles, and automate lifecycle management |
AWS configuration (in the AWS console)
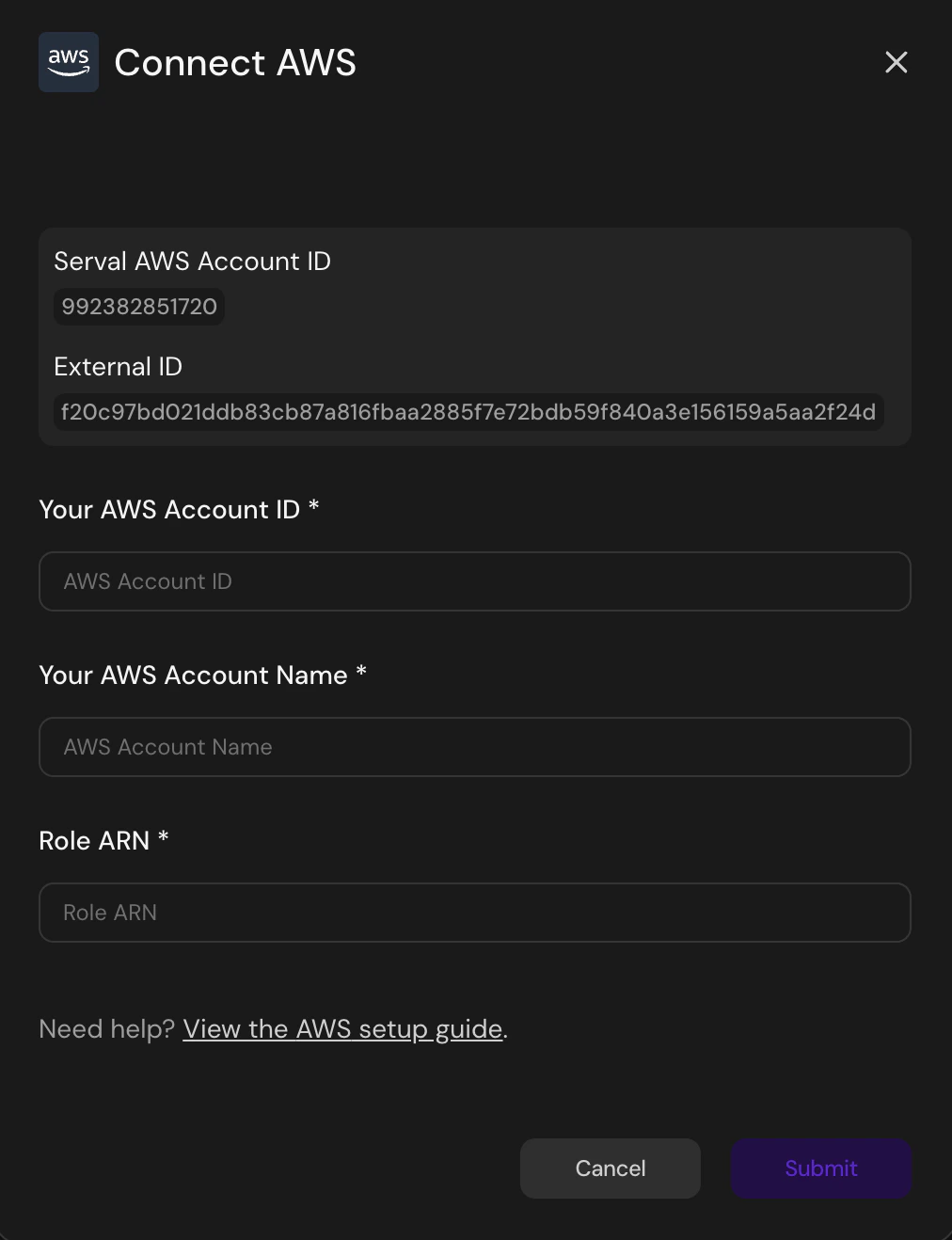
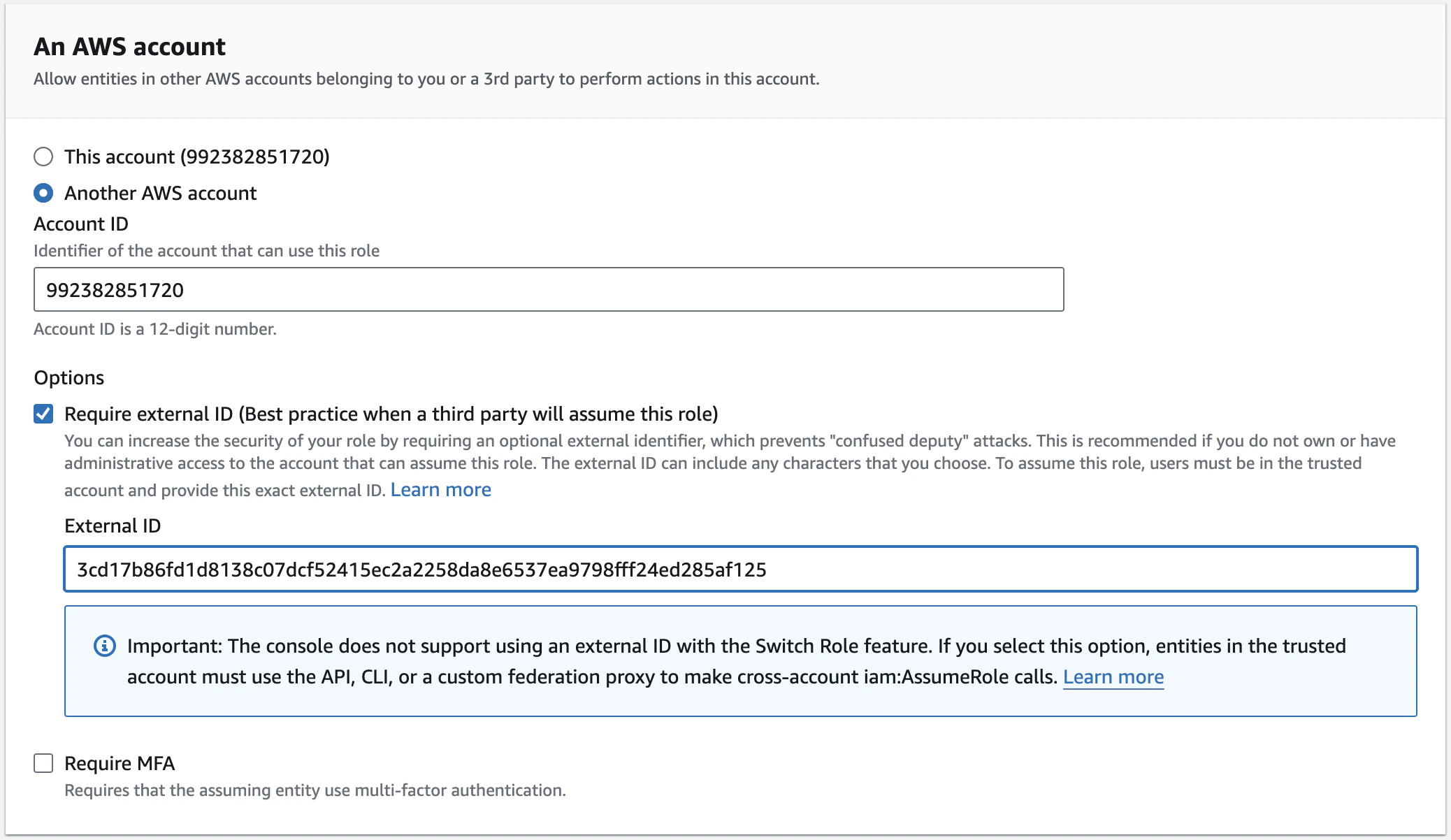
Follow these steps to create a cross-account role that Serval can assume. The role’s policies determine exactly which AWS APIs Serval can call.- Open the modal in Serval In the Serval UI navigate to Apps → Connect AWS. Leave this window open; it shows the Serval AWS Account ID and External ID you will need shortly.
- Create a new IAM role
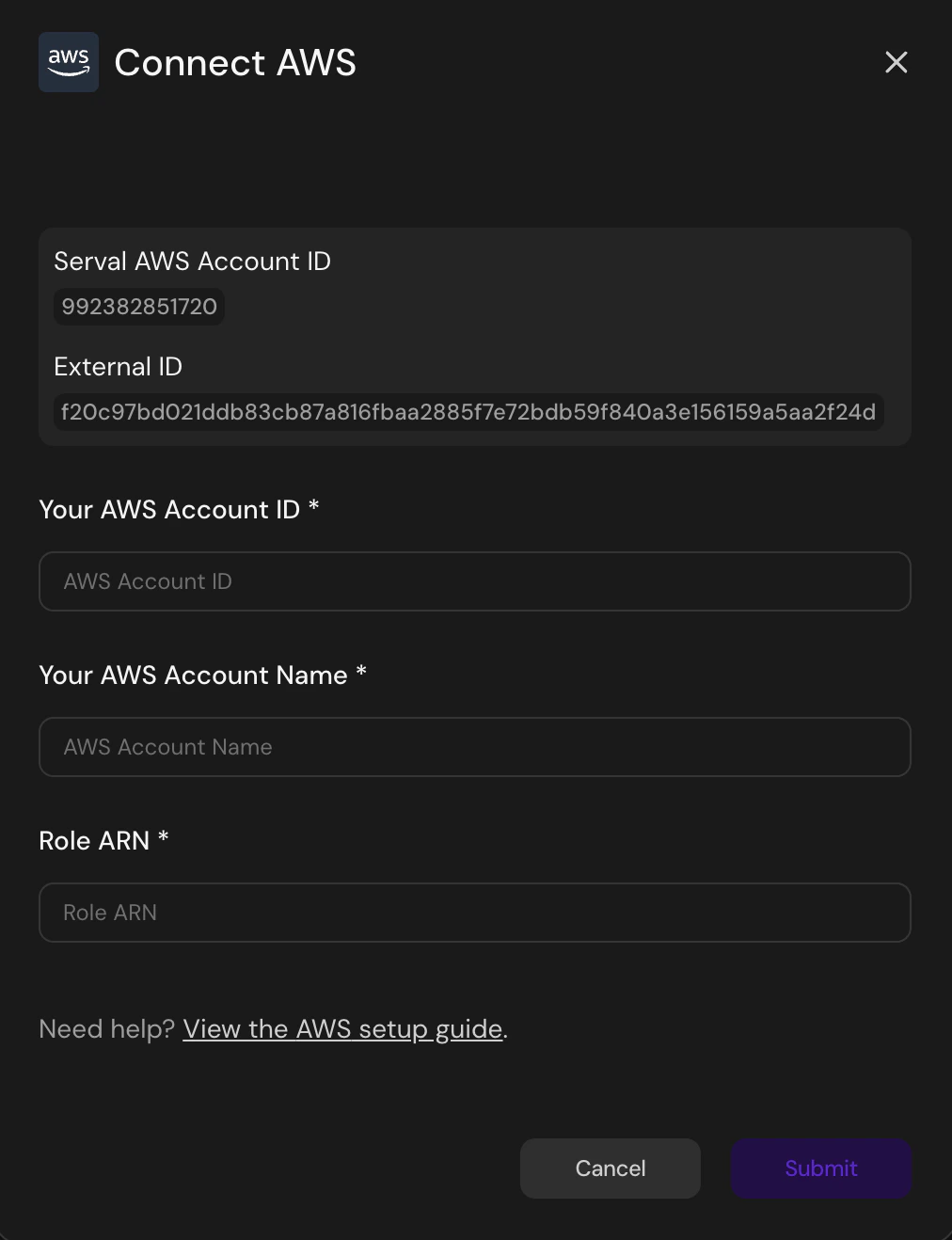
In AWS go to IAM → Roles → Create role and choose Another AWS account as the trusted entity.
Enter the Account ID shown in Serval, then tick Require external ID and paste the External ID.
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=228114b45b1f10a61ebf23fb3a90a410)
- Attach policies
Select AWS-managed or custom policies that grant the actions Serval needs (e.g.IAMReadOnlyAccess).
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=5ee36fe86472f8e8e5f86ce3bf9189a4)
- Finish the role wizard — name the role something memorable and click Create role.
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=48271df87fbaf2da4847761f777385e2)
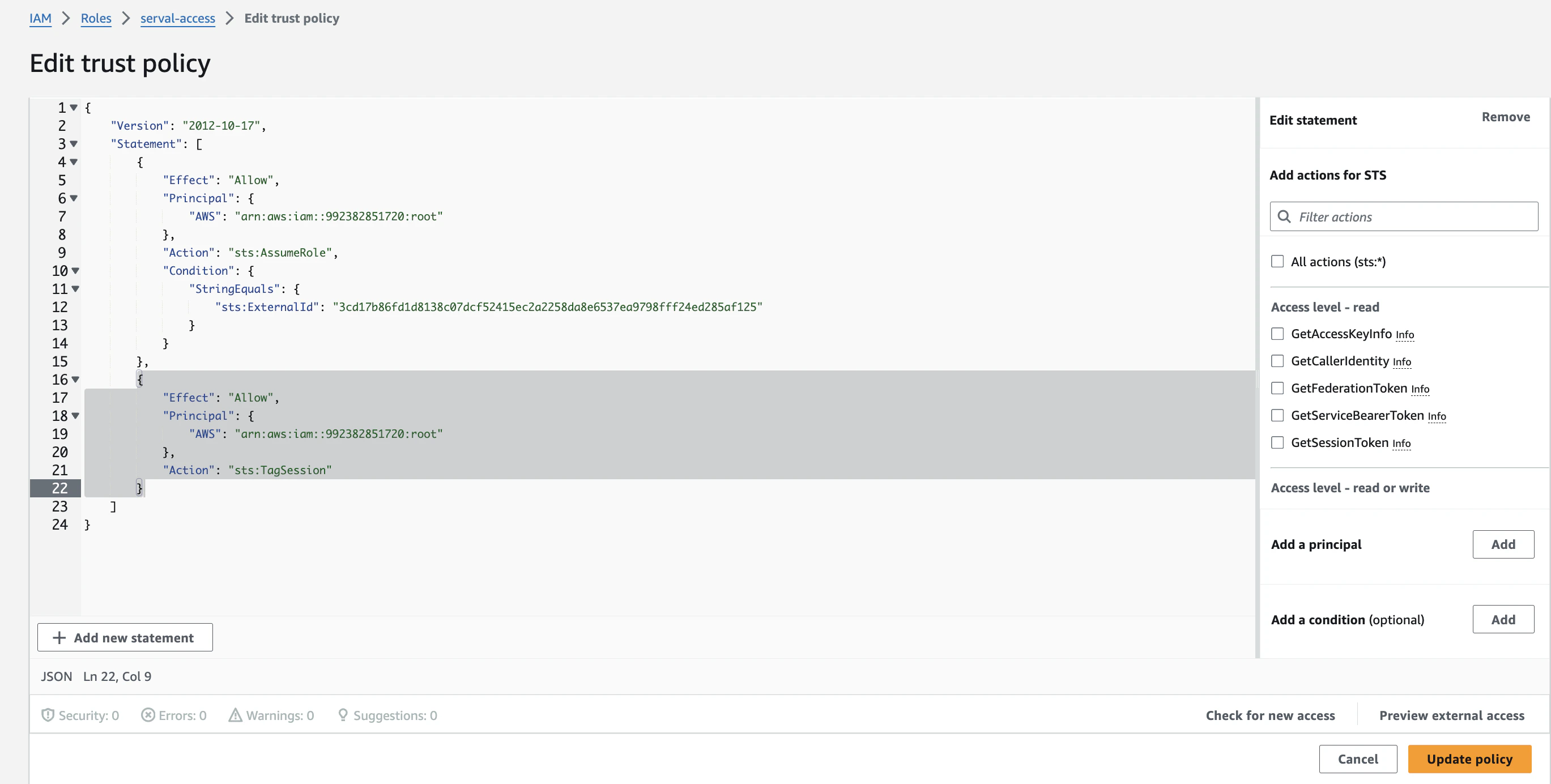
- Update the trust policy
Open the new role → Trust relationships → Edit trust policy and replace the document with the version below (adds the requiredsts:TagSessionaction).
.png?fit=max&auto=format&n=kEJkqsoMd8RKyAo5&q=85&s=864c27dd91e28a15eec148ba7945db24)
- Here is an example of the updated policy in the UI.
- Copy the Role ARN & Account ID — you will paste these into Serval in the next section.
Serval Configuration
- Return to the Connect AWS modal in Serval.
- Enter your AWS Account ID, a display name for the account (e.g. “Production” or “Sandbox”), and the Role ARN of the role you just created, then click Submit.
The Your AWS Account Name field is a human-readable label used to identify this AWS account within Serval. It does not affect the integration — you can enter any name that helps you distinguish between accounts.